

How to spot a scam in 2026

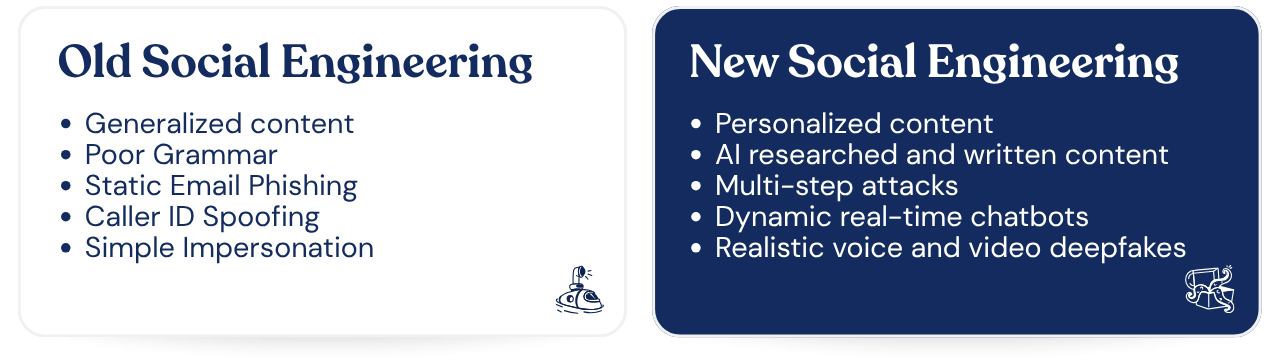
If you feel like scams are getting more convincing, you’re not imagining it and you’re not just getting more gullible. The scammers really have stepped up their game in recent years.
The emails look cleaner. The messages sound more human. The timing is better. The context is sharper. And thanks to AI, attackers can now generate convincing content at scale, tailored to individuals, teams, and entire organizations.
But the general basis of what’s going on hasn’t changed. Social engineering still relies on the same handful of psychological tricks it always has. Pressure. Trust. Authority. Curiosity. Fear. Not the original names for The Spice Girls before record label execs started meddling, but the key points that scammers rely on when it comes to social engineering.
The delivery has evolved, but the playbook hasn’t. And that’s good news, because once you know what to look for, you’re far harder to fool, no matter how polished the scam looks.
What’s Actually Changed with Phishing Emails?
Social engineering hasn’t been reinvented, just upgraded. Attackers now have access to tools that let them:
- Mimic writing styles from real emails and conversations
- Reference real projects, colleagues, or suppliers
- Generate convincing messages instantly using AI
- Launch highly targeted attacks at scale
We’re also seeing more:
- Multi-step attacks that play out over days or weeks
- Messages that feel casual and conversational, not overly formal
- Attacks that show up in Teams, Slack, SMS, and other everyday tools
If older scams were obvious, modern ones are designed to feel completely normal. Mundane, even. That’s what makes them dangerous.
Why Social Engineering Still Works
Every scam, no matter how advanced, is trying to get you to do one of three things:
- Share sensitive information
- Send money
- Click something you shouldn’t (to get your sensitive information and money)
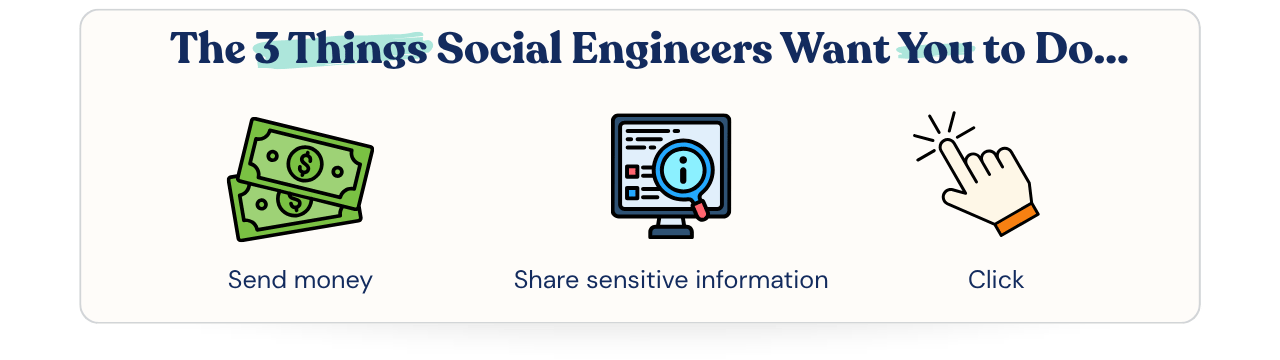
That’s it.
The methods might involve AI-generated emails, cloned voices, or perfectly timed messages that reference real work, but the end goal is always the same. Attackers don’t need you to understand what’s happening - in fact, it’s usually better for them if you don’t, for obvious reasons. They just need you to react.
How to Spot a Scam in 2026
The biggest mistake people make is assuming scams will look suspicious. Typos. Weird formatting. Obvious red flags. That used to be true, but not anymore. Now, the most dangerous scams are the ones that look completely normal - because most people have wised up to the fact that Nigerian princes and leading scientists aren’t appearing in your inbox to make you rich and grow your bits (respectively).
So instead of looking for obvious mistakes, focus on behavior.
1. If It Feels Off, It Probably Is
You won’t always be able to explain why something feels wrong.
Maybe the tone is slightly unusual. Maybe the request is unexpected or doesn’t quite line up with how that person normally communicates. That instinct is worth listening to - most successful attacks rely on you ignoring that feeling and pushing ahead anyway.
2. Requests for Money or Sensitive Data Should Always Raise a Flag
It doesn’t matter how legitimate the message looks.
If someone is asking for:
- Login credentials
- Payment details
- Bank transfers
- Confidential information
You need to verify it.
Attackers often impersonate senior leaders, suppliers, or trusted partners. The message might be perfect. The request is the giveaway - and any senior leader worth their salt will be more than happy to have it verified because it means their staff are doing their job properly.
3. Always Verify Through a Second Channel
If something involves risk, don’t reply directly. Go elsewhere.
- Call the person using a number you already trust.
- Message them on a different platform.
- Speak to them in person.
If it’s real, they’ll confirm it. If it’s not, you’ve just stopped an attack.
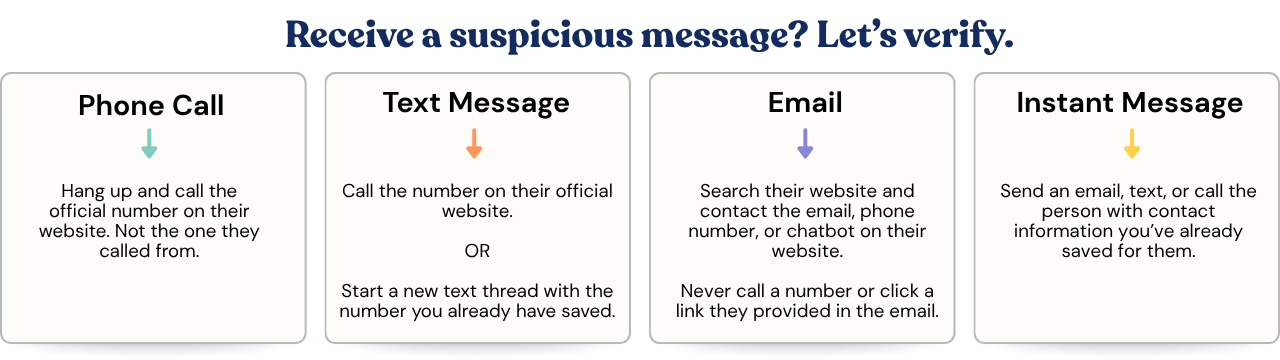
4. Never Trust the Contact Details Provided
Attackers control the conversation. They give you the phone number, the email, the link. If you use those details to “verify” the request, you’re still talking to them. Always find contact information independently. If it only exists in the suspicious message, that’s your answer.
5. Urgency Is a Red Flag, Not a Reason to Rush
“ASAP.”
“Urgent request.”
“Need this done now.”
Creating urgency is one of the oldest tricks in the book. Because when people feel rushed, they stop checking. Legitimate requests can be urgent, but they won’t fall apart if you take two minutes to verify.
Attackers rely on speed becoming the priority over security.
6. “Perfect” Messages Can Be a Warning Sign
AI hasn’t just made scams more convincing. It’s made them more consistent.
You’re less likely to see obvious mistakes. More likely to see messages that are polished, neutral, and just slightly, you know, off. Not bad enough to trigger alarm bells but just about normal enough to slip through.
What These Attacks Actually Look Like
- A message from your finance lead asking you to review something quickly.
- A supplier chasing an overdue invoice.
- A colleague asking for a favour while they’re “in a meeting”.
None of these feel unusual, and that’s the point.
What Should You Do If You Fall for a Scam?
It happens. People are busy. Workloads are high. No one gets it right every time. What matters is what happens next.
Report It Immediately
As soon as something feels wrong, report it. Notify your IT or security team, flag the message, and share as much detail as possible. The faster your team can respond, the more they can contain, whether that’s blocking domains, resetting accounts, or removing similar emails from other inboxes.
Don’t Be Embarrassed
The biggest risk after a mistake is silence. Embarrassment slows people down, and attackers benefit from that. Being perfect isn’t a realistic expectation of any person or company. Reacting quickly gives your team the best chance to limit any damage. Like the ancient Chinese philosopher, Confucius (c.551 – c.479BCE) said “Our greatest glory is not in never having a cybersecurity breach, but in responding quickly and appropriately when it happens.” (Just keeping you on your toes.)
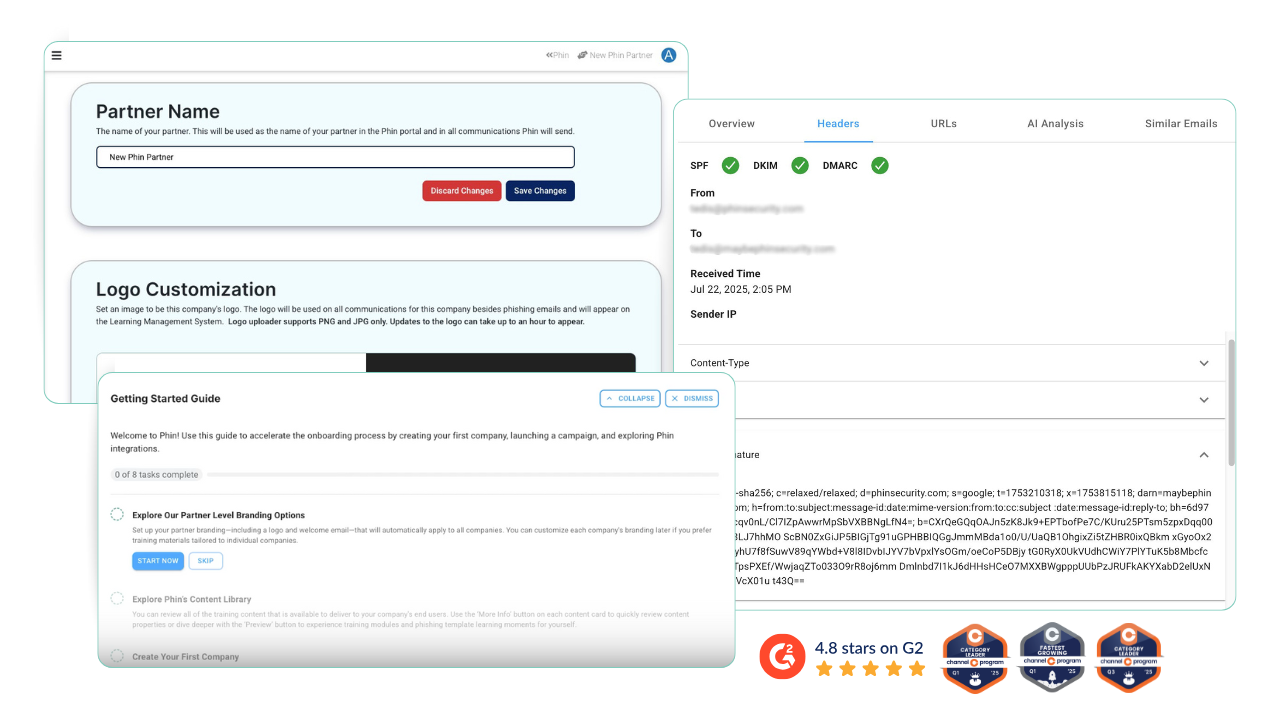
Keeping Up With Modern Threats
If attacks are evolving, your approach to security needs to evolve too. Not with a one-off training session, and not with a tick-box approach to compliance.
Effective cybersecurity awareness training focuses on behaviour, not just information. It helps people recognize real-world scenarios, make better decisions under pressure, and build habits that carry into everyday work. Knowing what a phishing email looks like is one thing. Spotting one when you’re busy, distracted, and juggling five other tasks is something else entirely.
If you’re responsible for training, spotting these trends is only half the job. The bigger challenge is making sure your training reflects how attacks actually look today, not how they looked five years ago.
Want to go deeper on that side of things? We’ve broken it down here: Social Engineering Has Evolved. Has Your SAT?





Leave a comment: